Joint Ukraine and Korean task force arrest Russian-linked hackers in Kiev after Joe Biden demanded a crackdown on groups launching cyber attacks on US networks -The group known as Cl0p, allegedly is behind multi-million ransom attacks on hundreds of US and Korean companies
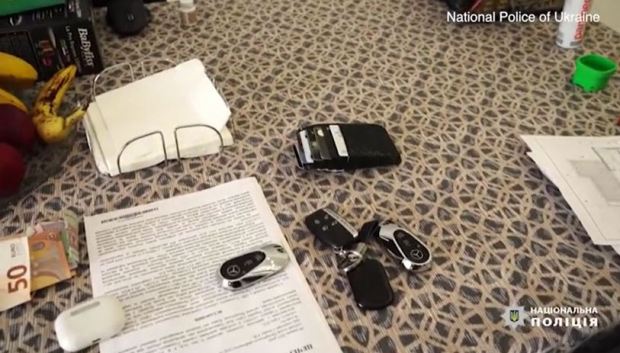
Ukraine National police in a joint operation with Korean police took own a Russian-linked hackers on Wednesday in the capital Kiev, seizing computers and electronic devices
Six members of the Russian-linked cyber hacking group Hackers, dubbed Cl0p, were arrested after police scaled the walls to a private estate home and used an electric saw to cut open the locks on the front door
Police also recovered $185,000 in cash and seized several expensive items including luxury cars
The raid came a day after President Joe Biden demanded a crackdown from Russia on the perpetrators of cyber crimes on US networks
The group, accused of attacking hundreds of companies including in the US and Korea like the attacks on Shell, Stanford University and University of California
In one case last year, they coerced a $6million Bitcoin ransom from one firm
Their attacks mirror those by other Russian-linked groups in recent months, including attacks on US companies like JBS meat processing plants and the Colonial Pipeline for a combined $15million in ransom
Ukraine’s action stands in stark contrast to Putin’s response when pressed by Joe Biden over hacking at their summit yesterday, which was to deny that Russia is the main source of cyber attacks on the US networks
The suspects have each been charged with hacking and money laundering, and are facing up to eight years in jail each

Ukraine has launched a major raid on a Russian-linked hacking network, based in the capital Kiev even as Vladimir Putin shrugged off president Joe Biden’s threat to get tough on cyber criminals.
Ukraine’s action stands in stark contrast to Putin’s response when pressed by Joe Biden over hacking at their summit yesterday, which was to deny that Russia is the main source of attacks on US computer networks.
The raiding party reportedly, seized dozens of computers and expensive cars in addition to about $185,000. The server infrastructure was taken down, and the homes were seized
The group as a whole is accused of attacking hundreds of companies including in the US and Korea, and last year was paid a $6million Bitcoin ransom by one firm.
In the last few months it has been reported, Cl0p hit dozens of victims, encrypting their files and demanding a ransom.
More recently, the hackers were trying to extort their victims by threatening to leak their files publicly on their dark web site, which displays 57 companies as of Wednesday.
Ukraine authorities released footage of major raid on Russian-linked hacking network C10p, seizing cash, computers and expensive cars
Ukraine announced the that the six people arrested are linked to the Cl0p hacking group which is accused of carrying out attacks on hundreds of firms including in the US. Police in Kiev did not name for fear of hurting their investigation.
The team also searched 21 addresses around the capital Kiev, seizing computers, cars and around 5million Ukrainian hryvnia, or $185,000.
Many cybersecurity watchers however, noted that the leak site used by Clop members is still up. Many do not believe the main players behind Cl0p were arrested in the raid because they live in Russia.
Those arrested were mostly involved in the money laundering end of the ransomware operation.
Cl0p is a hacking group described as ‘ruthless’, ‘sophisticated’, and ‘almost tireless’ by those who track it. Active since at least 2019, it is reputed to have launched attacks against hundreds of companies in that time.
It rose to prominence in 2020 after they demanded a ransom of more than $20 million from Software AG, one of the largest software companies in the world. Multiple cybersecurity companies have reported that Clop has ties to a malware distribution group named TA505 and a cybercrime group known as FIN11.
The suspects have each been charged with hacking and money laundering, and are facing up to eight years in jail each.

The group is responsible for some of the most headline-grabbing ransomware attacks seen over the last two years. Hundreds of victims range from Shell and Kroger to Stanford University, the University of Maryland, and the University of Colorado. Ukrainian police said the total damage done by their attacks amounts to an estimated $500 million.
Ukrainian police, accompanied by Korean officers, arrested six people on Wednesday accused of belonging to a hacking group known as Cl0p.
The Group’s modus operandi mirrors similar attacks by other Russian-linked groups in recent months, including the attacks on the JBS meat processing plants and the Colonial Pipeline.

They operate by installing a virus on a firm’s network which then harvests data and can be used to lock the system down. Hackers then issue a ransom demand to the afflicted firm, demanding cash to unlock the computers and/or prevent their data being leaked online.
The group’s dark-net site currently contains information from almost 60 firms including the likes of Shell, Stanford University, and the University of California.
Cl0p has been linked to Russia by security firm FireEye, which says the virus the hackers used has been designed to detect whether the computers it infects use Russian-language keyboards.
If they do, then the bug will destroy itself without causing any harm.
Experts say the fail-safe shows the groups are either working with the Russia state, or else have come to the understanding that as long as they don’t target the country, their activities will be allowed to continue.


Arrests were made on the same day Biden met with Putin and pressured him to take action against cybercriminals, a demand the Russian leader largely brushed off.
Experts have long believed that Cl0p has been operating out of the former Soviet bloc, likely with the blessing of the Russian state. Some data linked to the hackers is also written in the Russian language and they appear to stop working during Russian public holidays, FireEye added.
Cl0p’s methods mirror those used by other Russian-linked groups such as DarkSide, which the CIA blamed for the recent attack on the Colonial Pipeline.



The Colonial Pipeline Company revealed on May 7 that it had been hit by a ransomware attack that had forced it to take the pipeline – which supplies about half the east coast’s gasoline – offline.
It was only brought back online after the firm paid some $4.4million to hackers in Bitcoin, but still caused panic-buying and price hikes in some states.
Meat processing firm JBS was also hit by a similar attack two weeks ago, which shut down abattoirs in the US, Canada and Australia.
The firm has revealed that it paid some $11million to the hackers after the ‘sophisticated’ attack took all of its beef processing plants in the US offline for a day, threatening food shortages and price hikes.
FBI investigators subsequently blamed the attack on REvil, another group thought to operate out of eastern Euro with ties to Russia.


Another major security breach that was also linked to Russia was the SolarWinds hack in 2020, that compromised large sections of the US government, NATO, and other global bodies.
In response to the increasing attacks, G7 leaders including President Biden issued a joint statement following their meeting in Cornwall last week calling out Russia over its tactic backing of the hackers.
The statement specifically called on Putin to ‘identify, disrupt, and hold to account those within its borders who conduct ransomware attacks, abuse virtual currency to launder ransoms, and other cybercrimes.’

Putin has previously dismissed claims that attacks are being made by Russians or the Russian state as ‘farcical’.
After their recent face-to-face meeting, Biden has expressed a lack of confidence in Russia stepping up to the plate. Biden says he is hoping to use the threat of action by the US and its allies to force Putin to crack down.
‘I said what will change their behavior is if the rest of the world reacts to them and it diminishes their standing in the world. I’m not confident of anything. I’m just stating the facts,’ Biden said.



Leave a Reply